Safeguarding industrial management programs (ICS) from cyber threats is a important precedence, however remodeling these intentions into efficient actions may be difficult. Given the complexity of ICS and their networks, which regularly depend on outdated applied sciences and insufficient safety measures, it may be troublesome to find out the very best start line. Cisco Validated Designs (CVDs) are confirmed networking and safety reference architectures that industrial organizations can use to construct superior capabilities and create a versatile basis for the longer term.
The Cisco Validated Design for Industrial Safety has been up to date to create further blueprints for securing important infrastructure. Taking a phased strategy to safe the commercial community, the Cisco Industrial Risk Protection answer includes of OT asset visibility, zero belief entry and segmentation, and cross-domain detection, investigation and response.
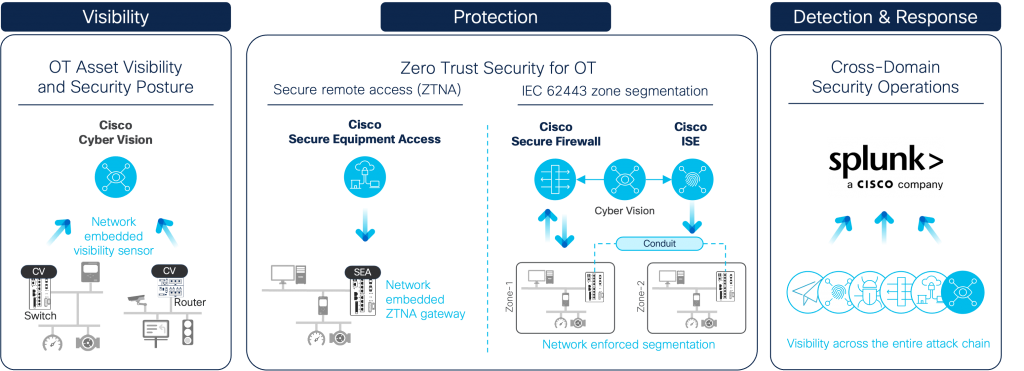
Cisco Industrial Risk Protection complete OT/ICS safety capabilities
Complete OT visibility driving community segmentation
The earlier model of Cisco’s Industrial Safety Validated Design described how the Cyber Imaginative and prescient sensor software program embedded in Cisco switches and routers may assist achieve visibility into related industrial property with out having to deploy devoted home equipment or SPAN assortment networks. It defined how management engineers and community managers may use this complete asset stock to implement adaptive zone segmentation within the industrial community by having Cyber Imaginative and prescient and Cisco Identification Providers Engine to seamlessly work collectively.
The up to date CVD now contains utilizing the Cisco Safe Firewall to safe plant networks. Rising investments into AI and the virtualization of the plant flooring is ensuing within the industrial information middle (IDC) turning into a important part of operational networks. Digital PLCs are an instance of this shift, the place digital controllers permit for a extra versatile and modular design of manufacturing crops.
In a conventional Purdue mannequin structure, the IDC would reside in stage 3, the commercial operations zone. However many operational networks who’ve carried out some ranges of community site visitors management have executed so on the IDMZ, or stage 3.5. Because the IDC turns into extra trendy, it additionally turns into extra related, counting on cloud connectivity for providers to run as meant. Extra connectivity expands the assault floor, so inserting the IDC behind a firewall is required to guard it if an assault was to breach the boundary firewall.
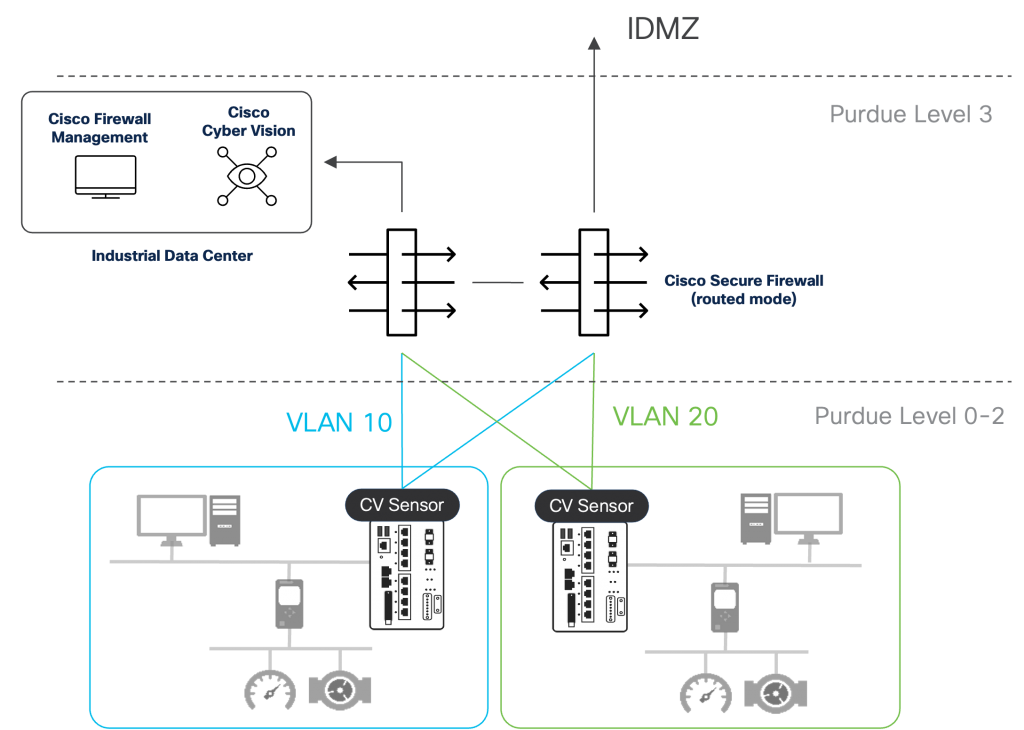
Cisco Safe Firewall for shielding the commercial information middle and segmenting OT networks
The Cisco Safe Firewall, supplemented by an integration with Cisco Cyber Imaginative and prescient, can be used to dynamically phase the commercial community and forestall cyber-attacks from spreading. The up to date CVD explains learn how to use the Cisco Safe Dynamic Attributes Connector (CSDAC) to make OT asset teams created in Cyber Imaginative and prescient routinely out there to the Firewall Administration Heart (FMC) as dynamic objects. Dynamic objects can simply be integrated into entry management insurance policies to permit or deny communications primarily based on supply/vacation spot, ports, protocols, and even Industrial Management System (ICS) instructions utilizing OpenAppID. Cisco Safe Firewalls put in within the industrial distribution body, or Purdue stage 3, will implement these entry insurance policies, driving east-west and north-south segmentation with the necessity to deploy devoted firewall home equipment in every zone.
A blueprint for securing distributed industrial infrastructure
The second main replace to the CVD gives design steering for constructing a cyber resilient community for distributed subject property with Cisco Industrial Routers. Whereas we regularly discuss so much about cybersecurity, which refers back to the strong instruments and insurance policies carried out to stop assaults from occurring in operational networks, we regularly overlook cyber resiliency. Cyber resiliency refers to an organizations means to take care of its important operations even within the face of cyber assaults.
Cybersecurity is in fact a part of a cyber resiliency structure. Capabilities reminiscent of firewalls, segmentation, and the implementation of a zero-trust mannequin implies that if an attacker does get a foothold within the community, their attain is restricted and each reconnaissance and lateral motion may be prevented. Nevertheless, cybersecurity practitioners and networking groups usually make the error of treating themselves as siloed entities within the group. The community configuration is simply as essential because the safety home equipment deployed within the community. High quality of Service (QoS) ensures that important site visitors all the time has precedence when the community is in a degraded state. Lossless redundancy protocols make sure that important site visitors meets latency metrics when community paths go down. Administration airplane safety ensures solely trusted customers get entry to the community infrastructure and can’t be taken down by malicious actors. Plug and play ensures that new community units are onboarded with a safe configuration out of the field. Whereas all these options are usually thought of a part of networking, it’s the mix of networking and safety that ends in a cyber resilient structure.
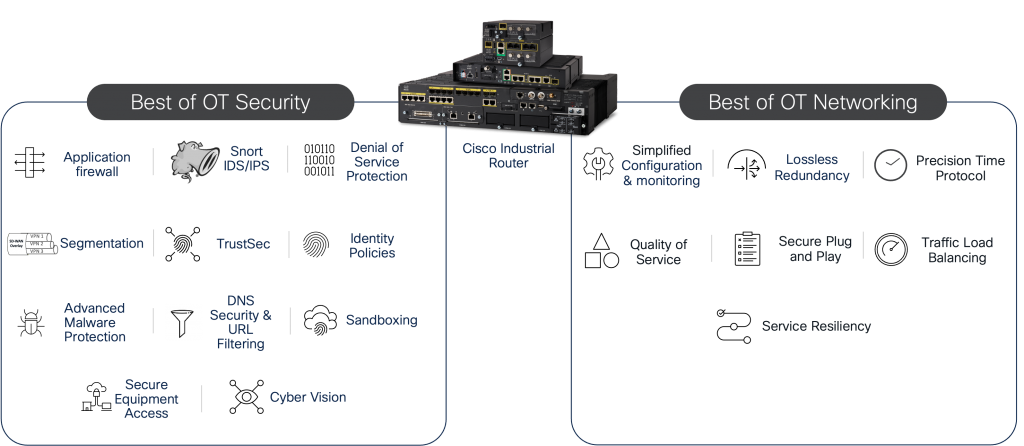
Cisco Industrial Router gives the very best of OT safety and rugged industrial networking
Zero belief distant entry made for OT
Final, however not least, the CVD explores the assorted choices for securing distant entry to industrial networks and describes learn how to deploy Cisco Safe Gear Entry to allow zero belief community entry (ZTNA) to the plant flooring. Distant entry options are available many types, and it may usually be complicated to grasp which one will meet enterprise wants. The design information compares digital personal networks, the distant desktop protocol, and the evolution in the direction of zero belief community entry, finally resulting in the deployment of Cisco SEA inside a Purdue mannequin structure.
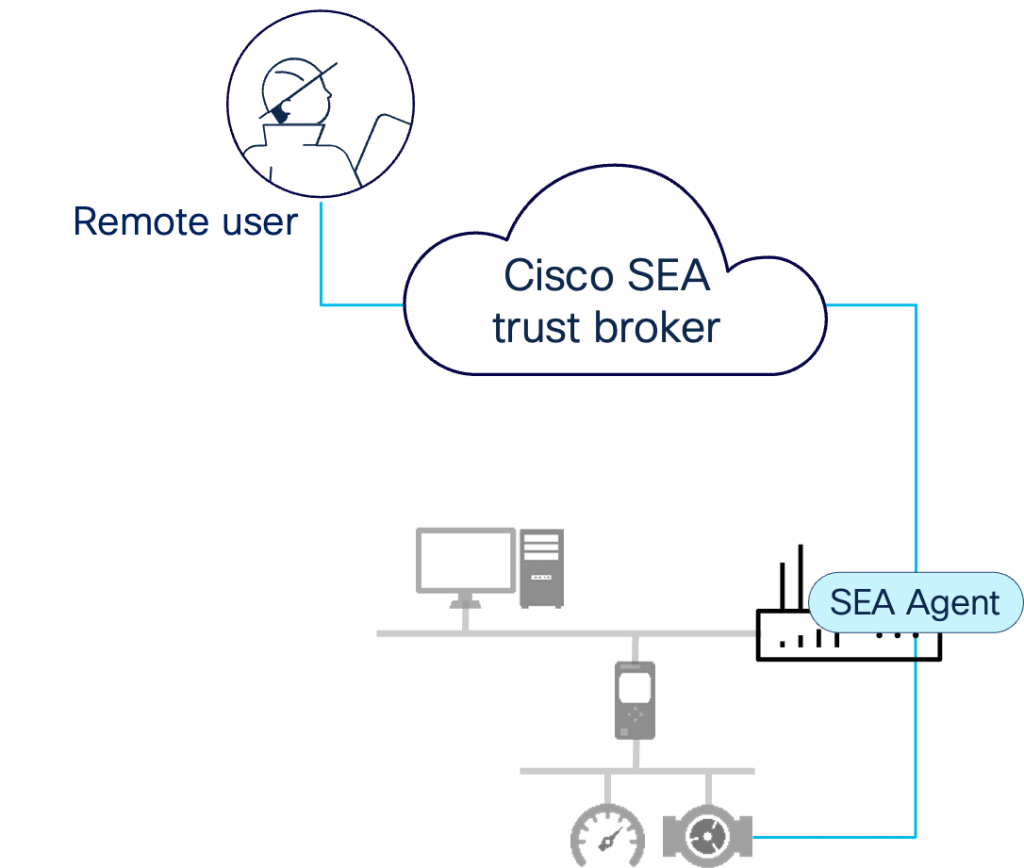
Cisco Safe Gear Entry permits ZTNA distant entry in industrial settings
Be taught Extra
The brand new model of the Cisco Industrial Safety Validated Design is accessible now. It’s free to assist everybody concerned in constructing and/or securing industrial networks to implement superior capabilities with out worry of integration complexities or efficiency surprises. For additional assist, flick thru a library of our industrial CVDs, or schedule a free, no-obligation session with a Cisco industrial safety professional, and we are going to attain out to you.
Share:

